OpenClaw Architecture - Part 4: Security Boundaries, Tool Risk, and Authorization
Why powerful agents get risky when authority crosses layers
Part 1 was about why OpenClaw feels alive: more inputs, durable state, and a loop.
Part 4 is the less glamorous follow-up.
Imagine a pretty normal setup. You give one shared operations agent a support inbox. You let it use a dedicated browser profile for an internal admin console. You give it enough session history to follow a case across turns.
Nothing exotic. Just enough to be useful.
A bad answer is annoying.
A bad action, taken through the wrong session or a real browser login, is a systems problem.
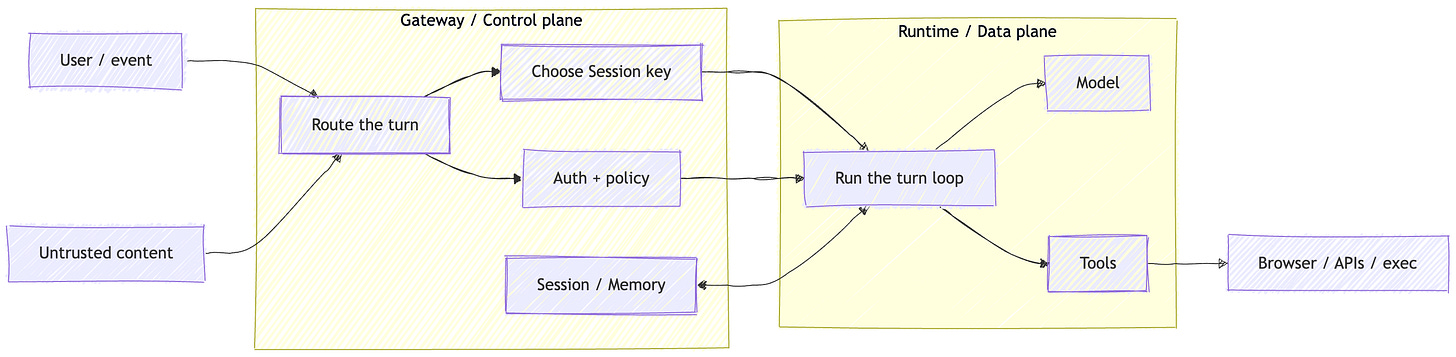
That is the security story here. Not whether the model can be made perfectly obedient. The real question is where authority lives, how the Gateway / Control plane routes it, and what the Runtime / Data plane is allowed to touch once a turn starts.
The model sits inside the loop, but the Gateway decides what state, policy, and capabilities that loop can reach.
The model isn’t the boundary
OpenClaw’s security guidance draws a useful line.
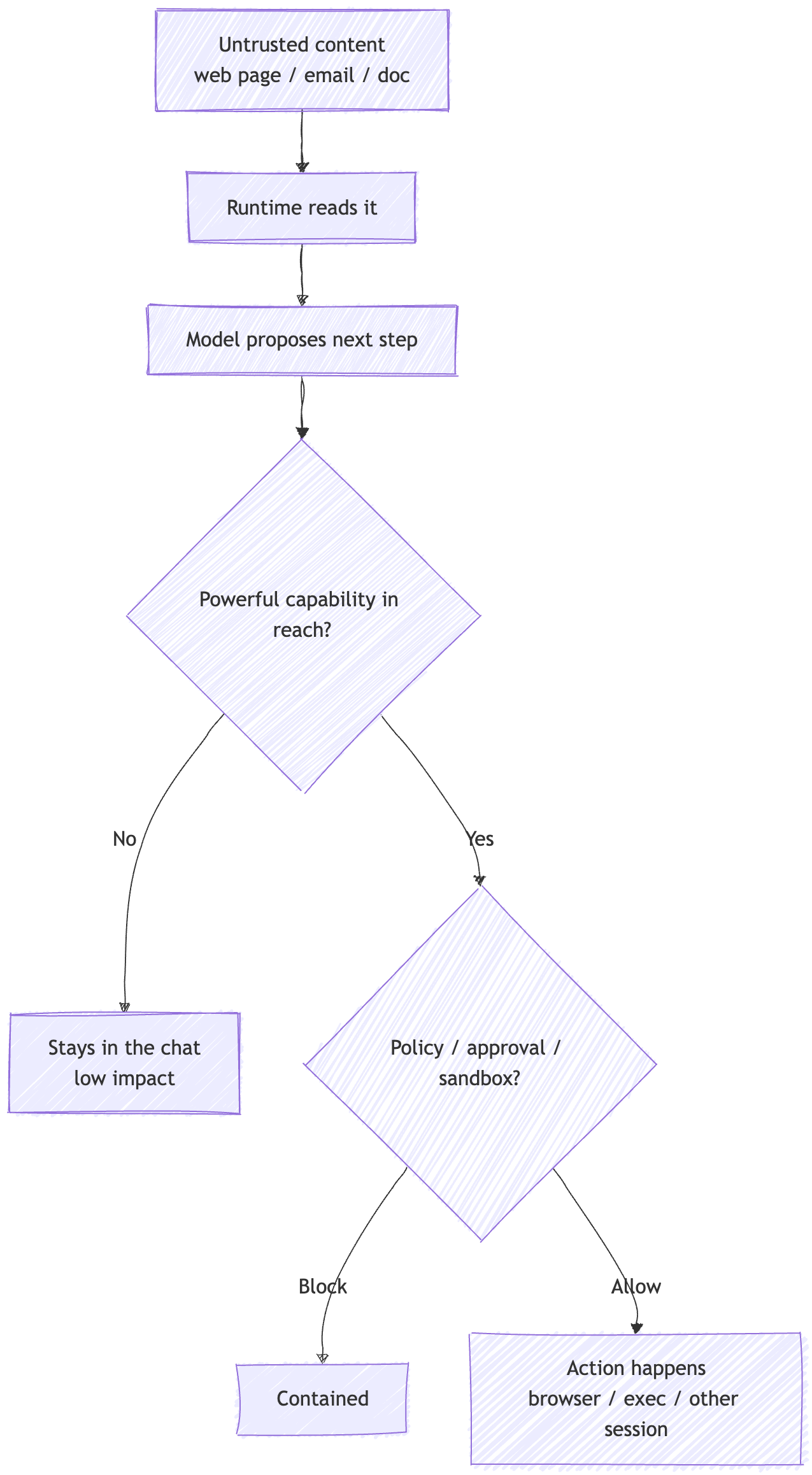
Prompt injection by itself is not the interesting category. It becomes a security problem when it crosses a real boundary: auth, policy, sandboxing, approval, or some other documented control.
That is a much better starting point than treating every strange model behavior like its own category of magic.
It also keeps the argument honest.
Of course the model can be influenced by input. That is not the surprising part. The question is what happens next. If untrusted content reaches the Runtime / Data plane, what authority can the system still spend on its behalf?
That is the part builders actually own.
Once you look at it that way, agent security gets less mystical. You are not mostly defending a prompt. You are defending boundaries around state, tools, identities, and who the system is willing to trust.
In that shared operations-agent setup, the risky step is not that a strange email contains adversarial text.
The risky step is that the same runtime may still have a path to an admin browser, cross-session tools, or other powerful surfaces after reading it.
Where authority actually lives
My read is that the Gateway / Control plane is the real security surface.
That is where OpenClaw keeps session state, applies auth and policy, exposes the admin surface, and decides which tools and routes are even in reach. The docs are explicit that authenticated gateway access is a trusted control-plane role inside one operator boundary, and that sessionKey, session IDs, and labels are routing selectors, not authorization tokens.
That sounds like a small distinction.
It is not.
A Session key tells OpenClaw which transcript and state bucket a turn belongs to. It does not answer who should be allowed to reach that bucket in the first place. If you blur those together, you end up treating routing like access control.
OpenClaw is also pretty direct about the trust model. One gateway is one trusted operator boundary. It is not trying to be a hostile multi-tenant bus where mutually adversarial users share one agent and get clean isolation from each other.
If you need that, the answer is to split the trust boundary: separate gateways, separate credentials, ideally separate OS users or hosts.
The Control UI makes the same point from another angle. It is not just “the web app.” It is an admin surface. If you expose it, or if you delegate auth to a reverse proxy, that is part of your security model, not a frontend detail.
If you cannot clearly say who is allowed to route into this session, this browser profile, this plugin surface, or this control-plane endpoint, the model is not your main problem.
When chat becomes action
This is the shift from chatbot to agent.
A chatbot can still do dumb things. Most of those failures stay inside the transcript.
An agent can leave the transcript.
In OpenClaw, that means the Runtime / Data plane can call tools, reuse browser state, inspect other sessions, or run code depending on how the system is configured. Session tools can fetch raw transcript history, send into another session, and spawn subagents. The browser may be logged into real accounts. Plugins can add tools, routes, and background services, and they run in-process with the Gateway.
That is why tools change the risk model.
A bad answer stays in the chat window. A bad tool call crosses a boundary.
The problem is not that the model saw bad input. The problem is what the system still lets it do afterward.
The browser docs make this concrete. The managed profile may contain logged-in sessions. Capabilities like browser evaluate and wait --fn execute JavaScript in the page context. Remote CDP endpoints are powerful and need to be treated that way.
Plugins are the same kind of story. They are not just extensions. They are trusted code running in-process with the Gateway. If you install them casually, you widen the control plane casually.
Once chat becomes action, you are not mostly managing output quality anymore.
You are managing delegated capability.
Sessions are a confidentiality surface
Part 1 treated sessions as an isolation mechanism.
Part 4 needs the more uncomfortable version of the same idea: session routing mistakes become confidentiality mistakes.
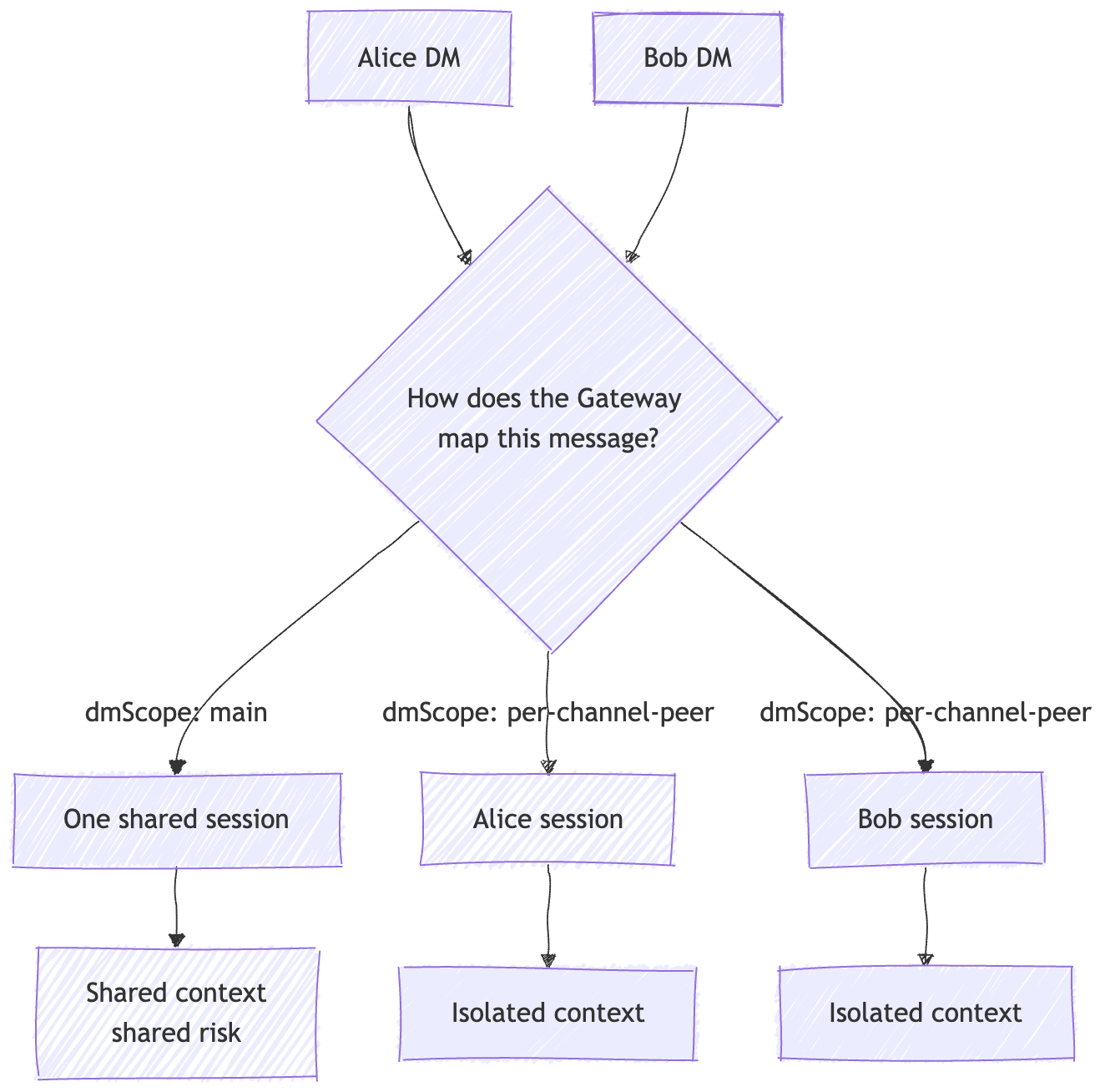
OpenClaw’s session docs make the simplest case clearly. With session.dmScope: "main", DMs collapse into one main session for continuity. That is fine for a single-user setup. It is not fine for a shared inbox. If more than one person can DM the agent, the docs recommend per-channel-peer or per-account-channel-peer so one sender’s context does not leak into another sender’s turn.
This is also a good place to separate two ideas that often get blurred together.
My read is that a lane / session lane preserves the single-writer invariant inside one session. It keeps two runs from trampling the same transcript at once.
That matters for correctness.
It is not the same thing as privacy.
A session lane keeps state ordered. It does not decide who should share that state.
The same goes for a global throttle lane. It can cap total concurrency across sessions. Useful for stability. Not an authorization system.
A session lane can keep one session sane, but privacy still depends on how the Gateway maps people into sessions.
OpenClaw’s session tools make the confidentiality angle hard to ignore. sessions_history can return raw transcript messages. sessions_send can inject a message into another session. And tools.sessions.visibility decides how far that surface reaches: self, tree, agent, or all.
That is not just convenience.
It is part of the read and write boundary around state.
Memory belongs here, but only briefly. It is the same problem stretched over time. Once state outlives a turn, it needs ownership, scope, and an explicit boundary around who can recall it. Part 3 covered the deeper version. The practical point here is simpler: sloppy session boundaries make durable state more dangerous.
The controls that actually matter
This is the unglamorous part.
It is also the useful part.
If the threat is boundary crossing, the controls have to live outside the model.
In OpenClaw, that means explicit access controls: pairing, sender allowlists, secure DM scoping, smaller tool surfaces, tighter session visibility, dedicated browser profiles, dedicated accounts, and treating the Control UI like the admin surface it is.
It also means being honest about deployment. Trusted-proxy auth can be reasonable. It is still part of your authorization path. A shared agent can be reasonable too. But if the same runtime or browser profile is signed into personal or overly broad accounts, you have already collapsed the boundary.
One thing I like about the docs is that they keep coming back to boring, real boundaries.
Dedicated machines.
Dedicated accounts.
Dedicated browser profiles.
Scoped tools.
Audit.
That is the right shape of advice for a system that can actually act.
My read is that this is the real mindset shift. Security here is not mostly about teaching the model better manners. It is about making sure the Runtime / Data plane cannot quietly inherit more authority than the operator intended.
Failure modes
Shared DM context by accident
The default dmScope stays on main. Two different people DM the same agent. One person is now steering context that was never meant to be shared. That is not a model failure. It is a Session key mapping failure.
Shared agent, shared credentials, wrong authority
A company-shared agent is signed into a personal browser profile or a broad internal account. Anyone inside that trust boundary can now steer the same external identity.
Cross-session transcript reach
Session visibility is broader than intended, or session tools are reachable too casually. Raw history becomes queryable, or messages can be injected into another session. That is not “memory magic.” It is an over-broad read/write surface.
Plugin installed like a feature, not like code
A plugin adds routes, tools, or background services and runs in-process with the Gateway. That is a control-plane trust decision, not a cosmetic extension.
Untrusted content plus broad tool access
External content reaches the Runtime, prompt injection happens, and the Runtime still has browser control, session tools, or other powerful capabilities in reach. The bug is not that text influenced the model. The bug is that the boundary after the model was too wide.
Builder checklist
Split trust boundaries at the Gateway / host / account layer. Do not ask one gateway to behave like a hostile multi-tenant boundary.
Treat
sessionKeyas routing only. Put real authorization somewhere else.Use per-peer or per-account DM scoping whenever more than one human can message the agent.
Keep browser, exec, and cross-session tools off broad untrusted-content paths unless you truly need them.
Treat
tools.sessions.visibilityas a security setting, not a convenience setting.Give shared agents dedicated machines, dedicated accounts, and dedicated browser profiles.
Treat plugins as trusted code and allowlist them.
Audit the control plane regularly, because that is where blast radius usually gets widened.
Recap
Part 1 explained why OpenClaw can feel alive.
Part 4 is the reminder that “alive” is not the interesting part.
Authority is.
The model is not the boundary. The Gateway / Control plane is where authority gets routed. The Runtime / Data plane is where that authority gets spent. Sessions and Memory matter because they are state. Tools matter because they turn text into action. And most of the real work lives in the boring parts: scopes, routing, dedicated identities, containment, and audit.
Part 5 stays on that seam and goes one layer deeper into tools, plugins, and capability boundaries: how chat becomes action, why extension surfaces carry so much risk, and how to design those surfaces without making the whole thing haunted.
References / further reading
This post leans primarily on OpenClaw’s official docs and source, with OWASP and NCSC used only for broader security framing.
OpenClaw security docs + SECURITY.md - OpenClaw’s trust model, real boundaries, and the project’s framing of prompt injection.
OpenClaw session management + session tools docs -
sessionKey,dmScope, transcript ownership, and session visibility.OpenClaw browser, exec, and plugin docs - Where tool use turns bad answers into bad actions.
OpenClaw formal verification + security audit docs - Assurance, bounded verification, and operator audit surfaces.
OpenClaw GitHub source + DeepWiki - Code paths plus DeepWiki is a good architectural map before diving into the repo.
OWASP + NCSC guidance on agent security and prompt injection - Broader framing on capability boundaries, least privilege, and prompt-injection risk.




Spot on — the real risk isn’t the model, it’s where authority actually lives once chat becomes action.
We built Lionguard as open-source middleware that sits exactly in that Gateway/Control plane and enforces the boundaries you describe: tool-result parsing, privilege engine, cross-session drift detection, and circuit breakers that actually trip.
Tested 12/12 against the vectors in the articles @toxsec has been posting — all blocked or flagged locally, zero API cost.
Full write-up + repo here:
https://awakenedintelligence.substack.com/p/openclaw-has-no-immune-system-so?r=58lc4j&utm_campaign=post&utm_medium=web
github.com/holmanholdings/lionguard
Appreciate the clarity on what builders actually own. Happy to see the ecosystem getting serious about this.
This architecture diagrams loks like archtocode.com